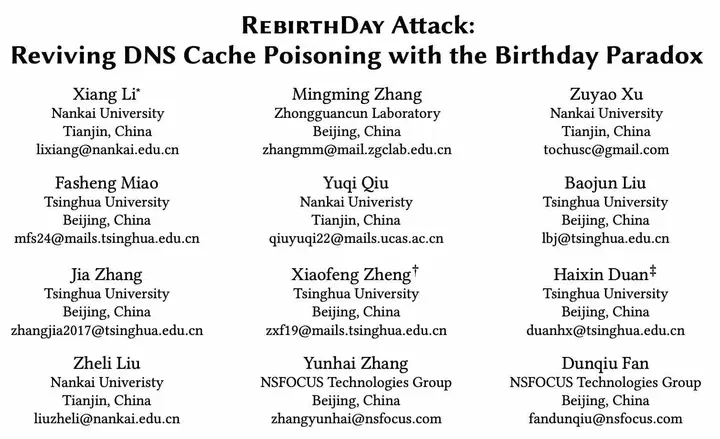
RebirthDay Attack: Reviving DNS Cache Poisoning with the Birthday Paradox
Abstract
DNS cache poisoning is a persistent game of attack and defense, posing an enduring challenge for the DNS community. Significant efforts have been made to uncover, detect, and mitigate vulnerabilities that increase the risk of cache poisoning. However, no work has systematically revisited whether the original cache poisoning attack based on the Birthday Paradox remains effective. In this work, we introduce RebirthDay, a novel DNS cache poisoning attack targeting recursive resolvers and forwarders, reviving the classic DNS Birthday attack that no longer works since 2002. RebirthDay exploits newly uncovered, protocol-compliant vulnerabilities in DNS extension implementations to bypass the query aggregation mechanism intended to prevent DNS Birthday attacks that has not been well understood. We uncovered that 18 out of 22 mainstream DNS software are vulnerable due to weaknesses in the processingof a DNS extension (i.e., ECS option), specifically lacking or incorrectly implemented ECS coherence checks when handling DNS queries and responses, demonstrating the widespread susceptibility to RebirthDay. These flaws could be exploited to circumvent thequery aggregation mechanism and launch RebirthDay attacks. Through comprehensive evaluation, we showed that RebirthDay attacks are highly practical and can have significant real-world impact, affecting 16 router vendors, 14 public DNS services, and 365K(15%) open DNS resolvers. We have reported the identified vulnerabilities to affected vendors and discussed mitigation solutions with them. To date, we have received acknowledgments from 8 vendors, including BIND, Unbound, PowerDNS, and Quad9, and have been assigned 50 CVE-ids. Our study emphasizes the need for greater attention to the importance of ECS verification and DNS extension implementations, revealing new security risks introduced by them.
Overview
RebirthDay, a novel DNS cache poisoning attack targeting recursive resolvers and forwarders, reviving the classic DNS Birthday attack that no longer works since 2002.
CVE/CNNVD (50/2)
-
2025: 13/2
-
2024: 37/0
-
BIND: CVE-2025-40776(High) CNNVD-202507-2228(High)
-
PowerDNS: CVE-2025-30192(High) CNNVD-202507-2635(High)
-
Unbound: CVE-2025-5994(High)
-
D-Link: CVE-2025-46663 CVE-2025-46665 CVE-2025-46668 CVE-2025-46671
-
Linksys: CVE-2025-46662 CVE-2025-46667
-
iKuai OS: CVE-2025-46666 CVE-2025-46670
-
RouterOS: CVE-2025-46664 CVE-2025-46669
-
Technitium: CVE-2024-56089(High)
-
HickoryDNS: CVE-2024-56099
-
Dnsmasq: CVE-2024-56097
-
CoreDNS: CVE-2024-56100
-
SmartDNS: CVE-2024-48980 CVE-2024-56088 CVE-2024-56090
-
DNSDist: CVE-2024-56092 CVE-2024-56094
-
Pi-hole: CVE-2024-56096
-
pdnsd: CVE-2024-56393
-
Acrylic DNS: CVE-2024-56095 CVE-2024-56098
-
AdGuard: CVE-2024-56091-CVE-2024-56093
-
AdGuard Home: CVE-2024-56101-CVE-2024-56106
-
DNS Safety: CVE-2024-56108
-
Dual DHCP DNS: CVE-2024-56102-CVE-2024-56103
-
NxFilter: CVE-2024-56104
-
YogaDNS: CVE-2024-56105-CVE-2024-56107
-
TP-Link: CVE-2024-56380 CVE-2024-56384 CVE-2024-56387 CVE-2024-56392
-
Mercury: CVE-2024-56382
-
Fast: CVE-2024-56381
-
Tenda: CVE-2024-56379
-
Redmi: CVE-2024-56385
-
Skyworth: CVE-2024-56383
-
Mercury: CVE-2024-56386
-
Fast: CVE-2024-56391
-
Netgear: CVE-2024-56388
-
Tenda: CVE-2024-56390
-
Fiberhome: CVE-2024-56389