Abstract
Public hosting services provide convenience for domain owners to build web applications with better scalability and security. However, if a domain name points to released service endpoints (e.g., nameservers allocated by a provider), adversaries can take over the domain by applying the same endpoints. Such a threat is called hosting-based domain takeover. There have been numerous domain takeover incidents in recent years that have had significant effects; even well-known websites like the subdomains of microsoft.com have been impacted. However, there is currently no effective detection system in place to identify these vulnerable domains on a large scale. In this paper, we present a novel framework, HostingChecker, for detecting domain takeovers. In comparison to previous works, HostingChecker expands the detection scope and improves the detection efficiency by: (i) systematically identifying vulnerable hosting services using a semi-automated method; and (ii) detecting vulnerable domains by passively reconstructing domain resolution chains. We evaluate the effectiveness of HostingChecker and eventually detect 10,351 subdomains from Tranco Top-1M apex domains vulnerable to domain takeover, which are over 8× more than previous findings. Specifically, HostingChecker enables us to detect the subdomains of Tranco sites on a daily basis. Furthermore, we conduct an in-depth security analysis on the affected vendors, like Amazon and Alibaba, and gain a suite of new insights, including flawed implementation of domain validation. We have responsibly reported issues to the security response centers of affected vendors, and some of them have adopted our mitigation.
In OARC 40 & NANOG 87 Workshop (hybrid in-person and online workshop), I presented a novel hosting-based domain takeover detection framework DareShark to the audiences.
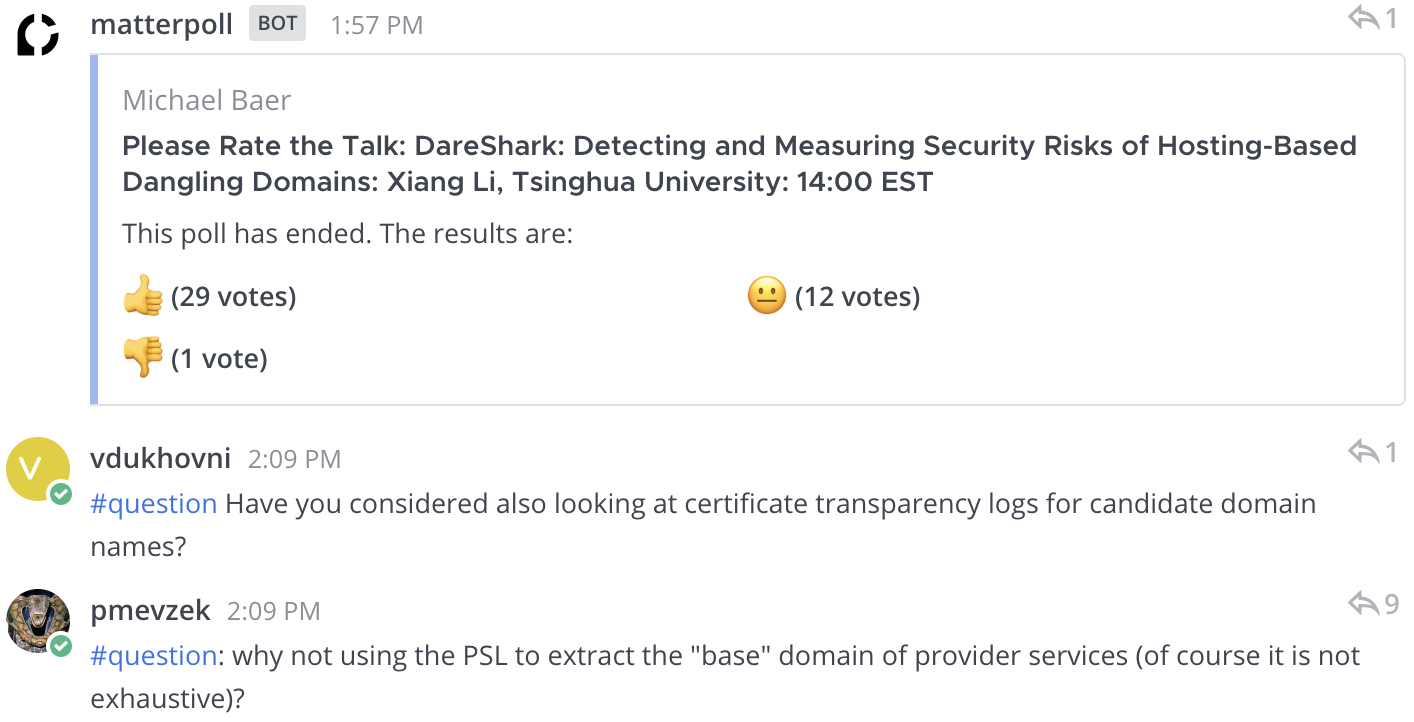
Feedback from workshops